
|
My Security Expert On-Call
When you do not have an IBM i security person on staff, we can be your IBM i Security Expert, On-Call.
Our On-Call service is a retainer-based service in which you can contact us when you have a security question or have a need for our security expertice.
Do you need us to participate in your auditor meetings? Need security monitoring service? Need someone to maintain your user accounts?
The number of hours per month/year are determined at the start of the service, as are service level response time agreements.
Customized Exit Programs for Network Access Control and Audit
|
|
|
Auditing and controlling network access through FTP, ODBC, Remote Command, Client Access File Transfer, and TELNET requires custom programming.
If you need to ensure all TELNET and FTP accesses are using SSL, a special custom written exit program can enforce that requirement. In addition, logging of network transactions is not provided by the operating system, so, a customized server exit program can provide the audit trail you need for audit and control purposes. We can write these customized network access exit programs for you.
Customized Exit Programs to Control and Audit CL Command Usage
When you need special controls for your Control Language commands, a custom exit program can be used. For example, if you want strict controls over who can create a library, or restore a library, a command exit program can provide as much granular control as required.
One customer, a large banking company, needed a command exit program to prohibit the creation of a printer output queue named QPRINT. Users could create any other output queue, but not QPRINT. We designed, coded, and implemented the CL command exit program that enforced that restriction.
Design, Build and Implement customized security programs and processes
When you have complex requirements for security related solutions, we can design, code, test and implement the custom solutions you need.
One customer, a large coffee company, needed a method to restrict Query users from accessing certain sensitive files. Even though the users had sufficient permissions to the files, they needed to be restricted to only a certain small set of files for use in the Query tool.
We provided the customized solution from design to implementation.
|

|
Setup and Configuration of 3rd party Security Software
We have significant experience with working with IBM i Security software from companies like SyncSort, Powertech, Cilasoft, Bytware, PentaSafe, Enforcive, SEA and SafeStone.
We can, in many cases, provide expert services on these software packages at a lower price point than provided by the individual vendors. |

|
To Discuss your requirements for Expert Security Services,
Call us at: 800.936.3140
or 314.932.2430
or send your email to:
info@SecureMyi.com |
|
|
|

|

|

|
|
|
Security Audit Service
The Security Audit Service is our most popular service. Whether you are preparing for your next SOX audit, or just want to understand the strengths and weaknesses of your current security posture, the Security Audit Service will provide the information you need to make informed decisions about your current risk profile.
The Security Audit service is typically a 5-day On-Site engagement in which we perform an in depth evaluation of the security implementation of your System i. The audit digs deeply into all aspects of the System i security configuration at the operating system, database and user interface level. Evaluation of user accounts, object permissions, database security and the various access methods are examined to determine the vulnerabilities and risk profile of the system. A comprehensive detailed document of all findings is provided as is an executive overview containing a list of high severity items and remediation recommendations.
The Network Security Assessment Service
This service is a sub-set of the Security Audit Service in which we examine your network access interfaces for proper logging, auditability, control and reporting capability. TCP/IP and SNA interfaces are examined for network vulnerabilities. ODBC, FTP, Remote Command, File Transfer, File Serving with NetServer are a few of the services that are evaluated in this assessment service. At the completion of the service, you receive a detailed document and a verbal presentation of the findings of the study, along with recommendations to audit and secure access through the network interfaces.
User Account Setup and Maintenance Assessment Service
This service is a sub-set of the Security Audit Service in which we examine the configuration of user accounts and methods used to maintain those accounts. One of the major problems we find in System i security implementations is the lack of defined processes in managing user accounts. Often, users are assigned inappropriate capabilities which can result in various vulnerabilities. The implementation of group profiles is also examined.
User account manitanance procedures may be lacking proper controls, as in the area of resetting Passwords, or in removing obsolete accounts. Various regulations and laws require timely deletion of obsolete accounts. At the completion of the service, you receive a detailed document and a verbal presentation of the findings of the study, along with recommendations to improve user account maintenance, and to assign proper groups, and capabilities consistent with the user requirements. We will also work with your staff to implement the recommendations.
The Object Level Security Assessment Service
This service is a sub-set of the Security Audit Service in which we examine the configuration of Library and Object level authorities(permissions). We often find that the Object level security configuration is not sufficient to provide the database integrity and protection needed to secure your business applications.
Often, 3rd party application vendors provide a very poor security model for their shipped software. You, the customer, are subject to that vendor's lack of security awareness.
In this service, we examine the object level security of your current applications, and provide a detailed document and verbal presentation of the findings. This includes the vulnerabilities found and potential alternatives to the current security schemes.
Remediation Services to repair security implementations
When you have determined that you have faulty security implementations in place, we provide the remediation services to repair the faulty implementation and work with you to implement the processes that will keep the system secure over time.
Upgrade Security Level to QSECURITY Level 40
Security level 20 and 30 have been shown to be insecure when used in a typical business environment. Several well publicized vulnerabilities exist in these security levels.
When you decide you want to move to a more resliient security level of 40 or 50, we can perform the process for you. With our proprietary tools and methods, we can help you make the move to QSECURITY level 40.
Security Event Monitoring and Reporting and Alert Services
We can set up your system to forward security realted events to our monitoring platform. So, in real-time, we can advise you of any hack attack, or other significant event.
We also offer a periodic check-up service in which we provide detail reports to you on events of interest on your system, such as authority failures, bad log-on attempts, File download events, etc.
Configuration of the Security Audit Journal QAUDJRN
The IBM i is capable of auditing many types of events occuring on your system. However, no monitoring will take place unless you have your system configured correctly. We will work with you to determine the events to be recorded and reported, and implement a regular reporting regimen to meet your audit requirements.
It is imperative that actions performed by powerul users are audited, and that the usage of sensitive commands is audited. Once audited, a reporting regimen must be implemented. We will work with you to configure these auditing tasks and to create the reports needed to meet your audit requirements.
Forensic Analysis of System and Security Related Events
Who deleted that file, and how and when did they do it? Who downloaded the Payroll file this week? When was this system setting changed, and by who, and how? Who changed that price in the price file? All of these events, and many more can be determined by an expert forensic analysis of the system.
We provide these detailed forensic evaluations, and can perform these services either on a retainer agreement or on a case-by-case basis.
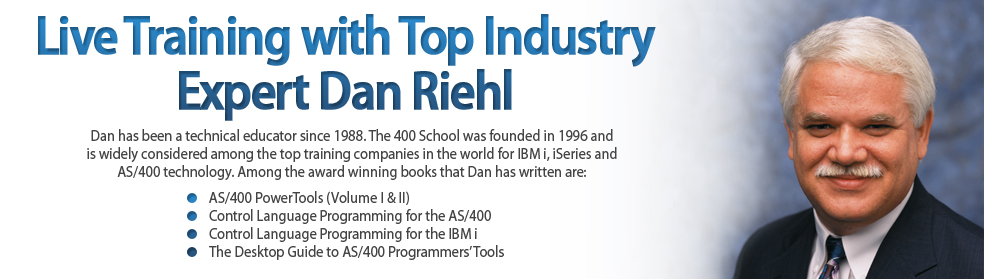
Live Hands-On Security and Audit Training by Dan Riehl

SecureMyi presents our training classes through our partner company, The 400 School. The 400 School has been training IT professionals for over 25 years in IBM i, iSeries and AS/400 technologies including System Security, System Administration, Computer Operations, and Programming in RPGIII and RPG IV, COBOL/400, and Control Language programming.
We always present our Training Courses LIVE, whether in our advanced Online Classroom for IBM i, or whether we come to your offices to present the finest in IBM i (iSeries, AS/400) training available anywhere.
We offer the following classes at your offices, or in our Online classroom. Click to view the class outline/agenda and any prerequisites.
|
|
|
|
|
|

